7 Mistakes To Avoid When Creating A Power Platform Environment

Setting up a Power Platform environment the wrong way can have serious consequences. This includes data-loss with no recovery from backups, lack of security that allows undesired users into the environment, and poor performance that hurts end-users efficiency. In this article I will show you how to properly setup
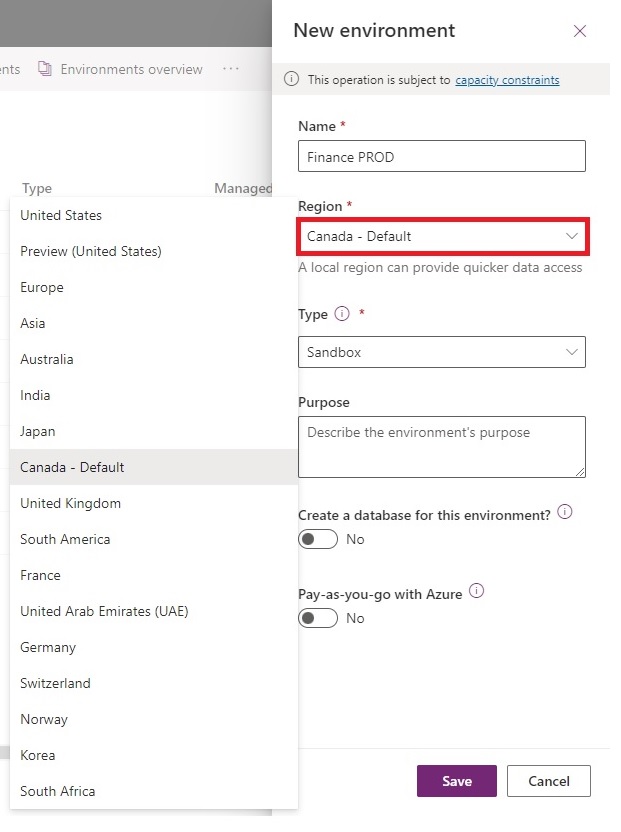
1. Picking The Incorrect Region
You only have one chance to select the proper region. If you choose the wrong one, there is no way to change it. The only way forward is to create another new environment and start again.
The environment’s region matters because it determines which datacenter your Power Apps, Power Automate flows and your data lives in. Choose the datacenter closest to your users to deliver the best performance. Also consider data sovereignty – data stored outside of your home country will be subject to the laws where it is stored.
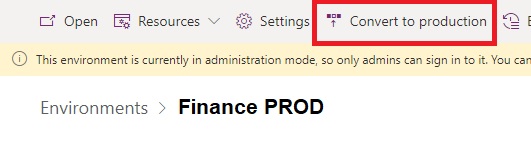
2. Choosing The Wrong Environment Type
The default environment type Sandbox enables the Reset action which deletes all data & customizations within the environment and restores it to factory settings. You cannot perform a restore to recover lost data or customizations because the environment backups get deleted too. It is critical that you make sure the environments used for production do not have the type Sandbox.
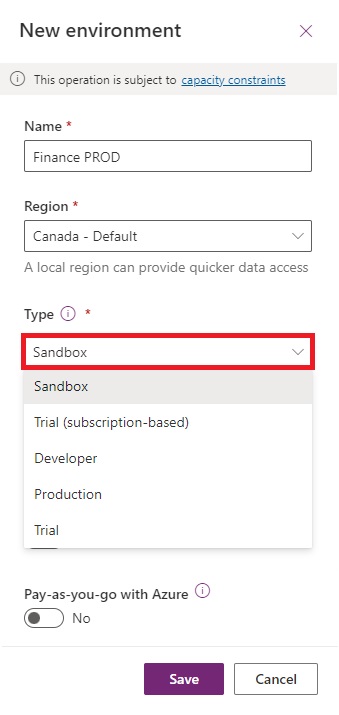
This mistake can be easily fixed by opening the environment in the Power Platform Admin Center and pressing the Convert To Production action.
3. Forgetting To Enter An Environment URL
Changing the environment URL after initial environment setup has the potential to break Power Automate flows and other customizations. For example, a Power Automate flow that uses the environment URL stored in an environment variable would begin to fail.
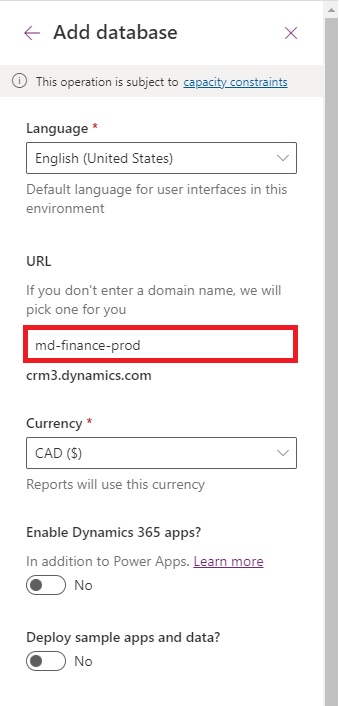
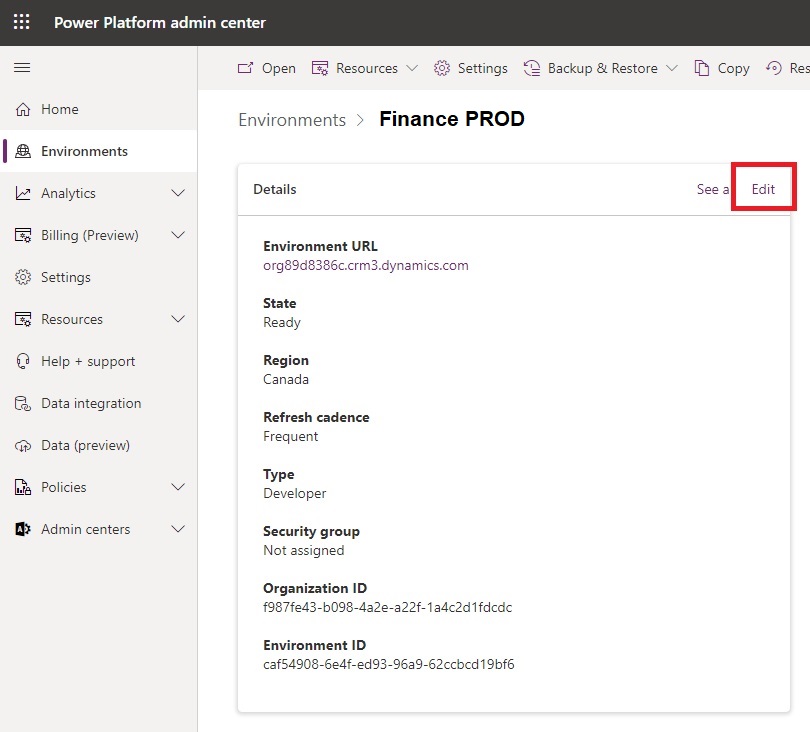
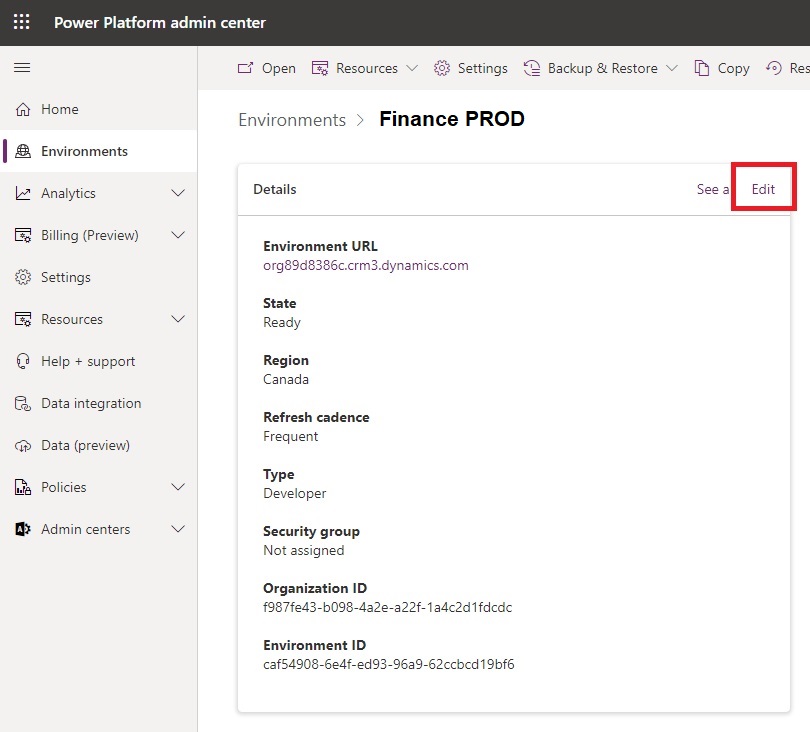
To update the environment URL after an environment is created go to Power Platform Admin center and Edit the environment settings.
4. Failing To Apply A Security Group
An environment with no security group allows the system administrator to assign roles and share apps & flows with any user in the tenant. Only developers should be allowed in the development environments to ensure no customizations are broken. Likewise, only authorized users should be allowed in the production environment to make certain no sensitive data is leaked.
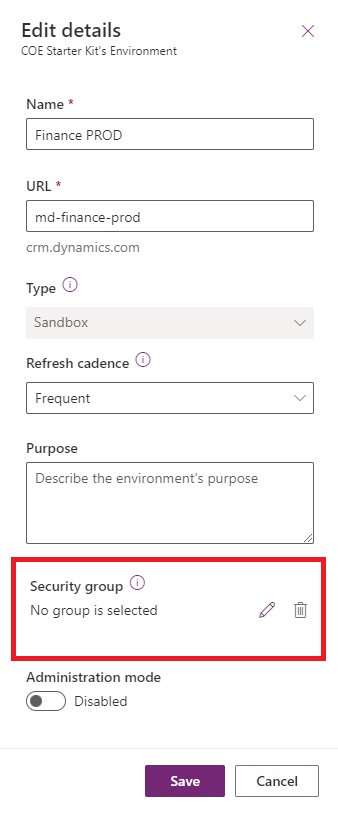
To update the Security group go to Power Platform Admin center and Edit the environment settings.
5. Missing Security Roles Assignment To Users
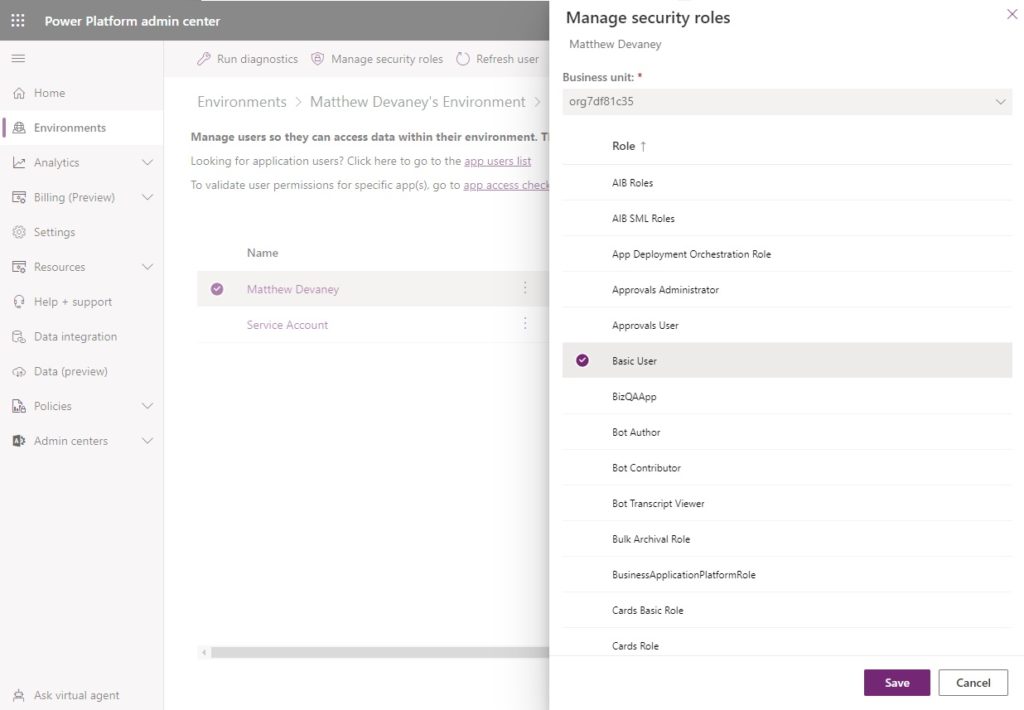
Users cannot run apps in an environment until they are assigned at least a Basic User security role. Developers require an Environment Maker role or System Customizer role to create new resources and view data. Additional custom security roles may be required as well. Do not assume that because a user appears in the environment’s Users list that they have a security role.
To assign a security role to a user, open the Users menu, select a user and then click Manage Security Roles.
6. Neglecting The Setup Of Data Policies
Data policies define which connectors are enabled or blocked and which connectors can be used with one another. By default all connectors can be used with no limitations. Your organization’s private data can be sent to 3rd party online services and consumed by their APIs.
If proper data policy for the environment is unknown upon creation consider move all Microsoft connectors to the business category while leaving the others in the non-business category. This will prevent Microsoft connectors from interacting with 3rd party APIs. Consider blocking the HTTP connector until you have a good reason to enable it. The HTTP connector can access any API on the internet.
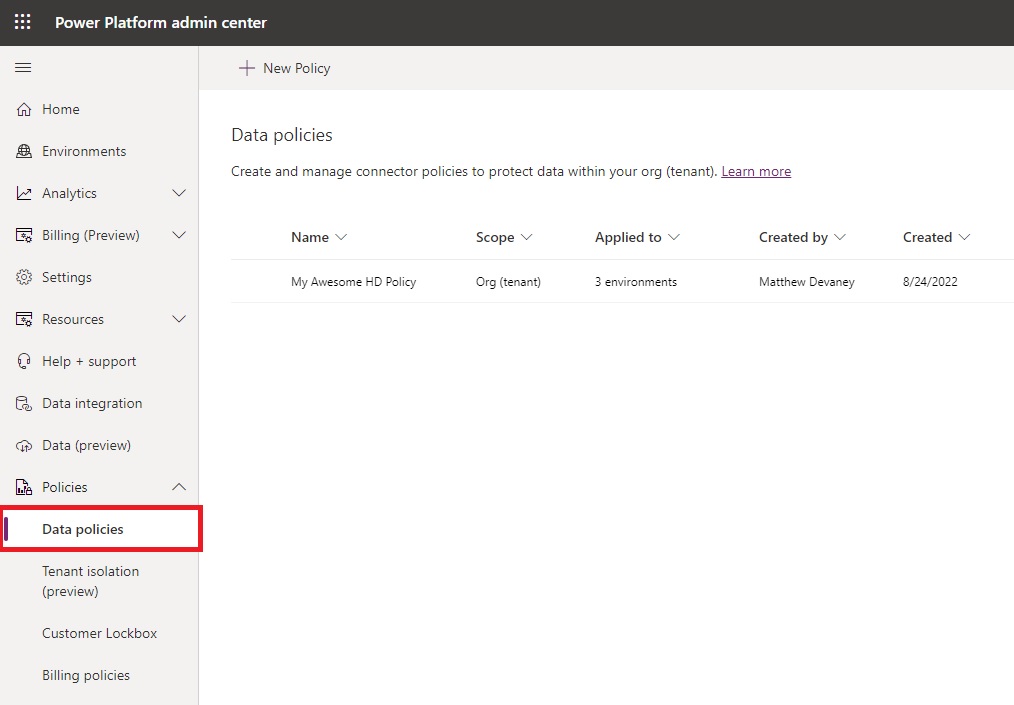
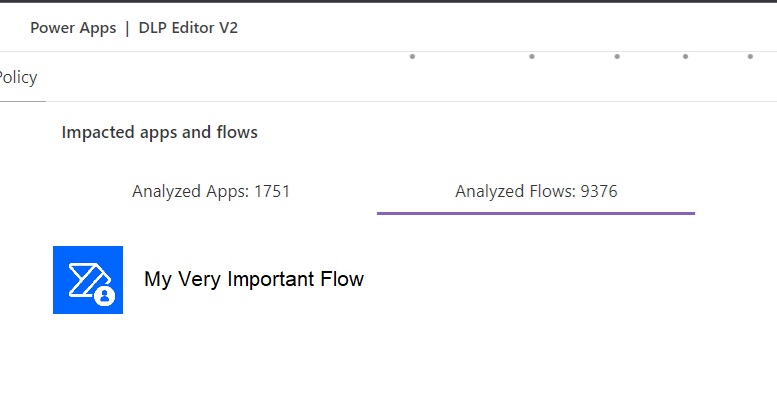
Also, if you decide to enact a data policy after apps & flows have already been developed, you run the risk of breaking them. The Power Platform Center Of Excellence Starter Kit includes a useful Power Apps app named DLP Editor. You can run an impact analysis before changing the data policy to see which specific apps & flows will break. Then you would inform their creators and find a resolution.
7. Delaying Applying Power Platform Licenses
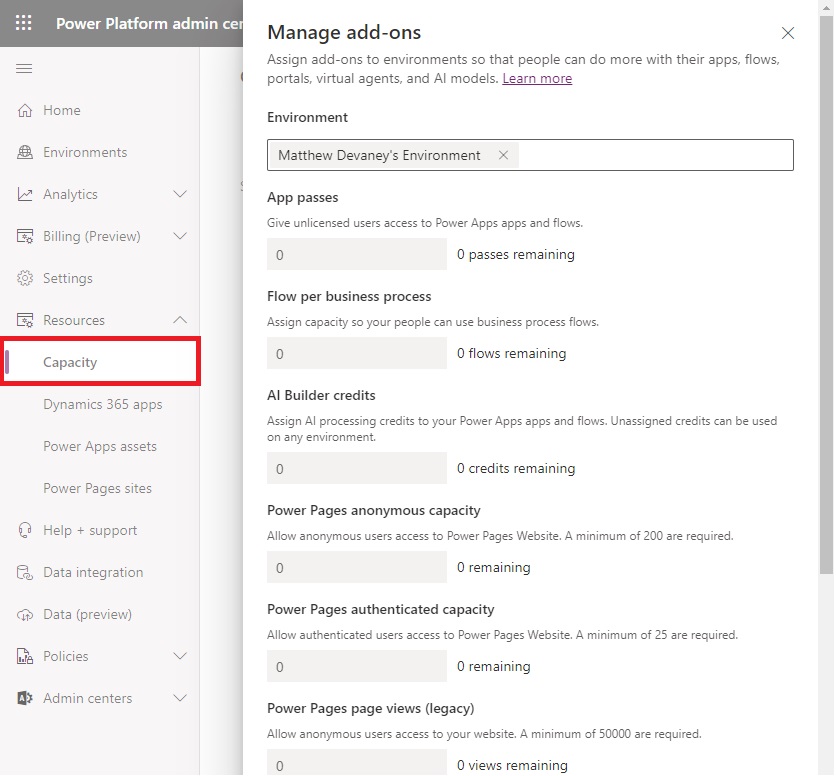
Developers and end-users alike cannot use being using premium apps, flows and other services without Power Platform licensing. Per app and per flow licenses must be added to the environment as an add-on within the Capacity menu. The sames goes for AI Builder credits and Power Pages capacity.
Per user licenses are assigned to a user account and do not need to be assigned to each new environment created.
Did You Enjoy This Article? 😺
Subscribe to get new Copilot Studio articles sent to your inbox each week for FREE
Questions?
If you have any questions or feedback about 7 Mistakes To Avoid When Creating A Power Platform Environment please leave a message in the comments section below. You can post using your email address and are not required to create an account to join the discussion.




Great post Matthew, thanks a lot. 🙂
Really helped me to check if my environments are in a good shape.
Bastian,
I’m glad you found it helpful 🙂
This email arrived as I sat down to work on exactly this issue. Absolutely essential reading which saved me a lot of time. As usual Mathew, you are a ray of sunshine. Thank you.
Great timing as I just had to do this for a client. I wonder what your thoughts are on creating a service principal for a brand new client? I go back and forth on if it would help with flow development or be unnecessarily complex. Thoughts?
Great article, very helpful for sure. Just got a question, how can we change the environment’s region after it was created? This doesn’t seem to be a simple task, I’d appreciate any info you can share. Thanks.
Edwin,
The first sentence in the paragraph about selecting the region says “you cannot change it.” As I said in the article, I can’t help you with this.
In our last project we need to install Dynamics Marketing into a previously created Power App environment. This was not possible. Have you got similar experiences?
Arghh i forgot to change the url by an explicit name.
Hi Matthew,
For development and testing environments would you recommend using environment type Production or Sandbox?
My concern is we now have a lot of unmanaged solutions in our dev environment – if someone was to hit that reset button……
Dan,
Dev and test should always be Sandbox. The Reset button will not be a concern if you are backing up your solutions in source control (GitHub, Azure Dev Ops Repos) and using a pipeline for deployments.
Thanks for your response – much appreciated. We are using the Power App Pipelines that ship with the product (Host environment) and I don’t think that supports source control?
Hello Matthew. Could you please share the approach on if we need to have several security groups connected to the environment with different roles?
Particularly I added two Teams in the environment each with a different group – one Entra AD and one M365 group. I applied same security roles, except one of the groups I also added Approvals User role. Will the users in both of these groups be added to dataverse? I ran into an error when using Approval action in Flow as follows: While testing, I received this error in the Approval action step:
The request failed. Error code: ‘UserNotMemberOfCdsSecurityGroup’. Error Message: ‘The user ‘########-####-####-####-############’ cannot be created in Microsoft Dataverse because the account is not a member of group ‘########-####-####-####-############’. Please ask an administrator to add user to the group.’.
Good day Matthew. I found the answer to my question from a colleague at another company. I had to remove the security group from the environment when I created it. Then verified each of the two teams I created with separate groups and security roles applied.
Beth,
Ah, glad to hear you found the answer Beth. Apologies that I was unable to follow up in a timely fashion.
As a Power Platform Administrator, these points are indeed helpful as a reference for every administrator in taking care of an organization’s Power Platform tenant. I’ve had a great review and things to note to make sure our organization’s tenant is properly managed.
Thank you for this, Matthew.
Janus,
You are very welcome 🙂
Hello, my environment gives by default Basic User Security Role to everyone and if I remove it the appear again, it is the default environment but it is a pain in the ass to check every 2-3 days that it does not give by default basic user security role to anyone. Any suggests?
Any ideas want to do ALM and build solutions containing apps, flow, SPO list etc. I have created the environments but try and build anything the environment cannot see anything like spo sites, forms, teams etc etc or anything in the default environment, any suggestions?
Matt,
SharePoint lists are not supported by solutions. You must do this manually each deployment or write a PowerShell script.
@Matthew Devaney It resolved itself It took longer than expect to propagate around as the GA account saw everything straight away where as service accounts etc took slightly longer than expected. So now when I build apps and flows I can see and point to lists in the default environment.
Good succinct info. Wish the microsoft forums were as efficient as this
I`ve a customer that want to deploy 7 version of the same Solution in same Environment (7 different plants will use each one a version), can he create 7 different environments without database? ( the solution use SharePoint as database )
Are there any known issues for changing a Power Automate accounts regional setting from US to UK?